iOS 15 Jailbreak
We have listed the all working iOS 15 Jailbreak tools and solutions for every iPhone and iPad models. These are working with minor versions of iOS 15.0.1 & iOS 15.0.2 too.
We highly recommend choosing the best one for your device, out of all iOS 15 jailbreak methods.
If you have upgraded to newer iOS versions, refer to the latest iOS 18 jailbreak page or iOS 26 jailbreak page for updated jailbreak solutions. For older devices, you can check the iOS 14 jailbreak page for previous compatibility.
1. Zeon
Zeon is an iOS 15 Jailbreak repo extractor that allows you to extract Jailbreak repos to install Jailbreak apps, themes, and tweaks. It’s a very easy online method, no need for computer support at all. Zeon is compatible with all iOS 15 and higher versions up to iOS 15.8.7.

How does Zeon Work
Tap the above button to download zeon directly to your iPhone or iPad. It has a very easy installation process with very few steps. After installation completes, open the Zeon app. Now you can install any number of repositories from Zeon.
Tap the Get Repo tab. Copy any repo, which you want to install. Tap the Repo Extractor tab. Paste the copied repo url there. Click ok to extract the repo. Then install the extracted repo to your iDevice.
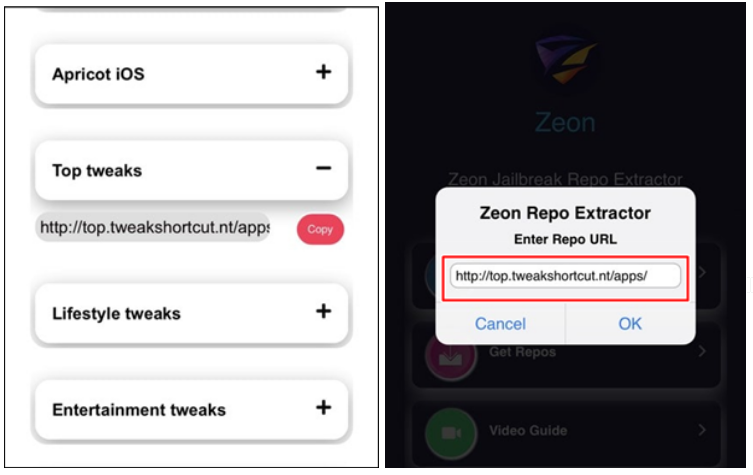
Watch Zeon repo extractor video.
More about Zeon
- Zeon is compatible for all device models, but we highly recommend it for latest iOS device models such as iPhone 14 models, iPhone 13 models.
- It’s compatible with all iOS 15 and higher device models. Refer more from Jailbreak iOS 15.5 page.
- You can install Cydia using ‘ios.cyrepo.tk/repo’ repo of Zeon or you can install Sileo using ‘ios.sileo.in./repo’ repo of zeon
- 100% risk-free if you install repos from the recommended list
- Your Apple software warranty is safe with Zeon
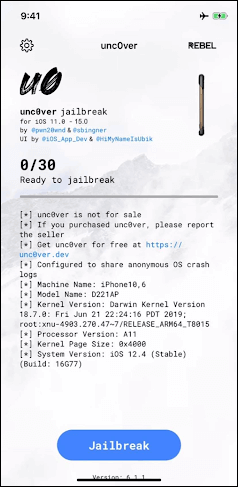
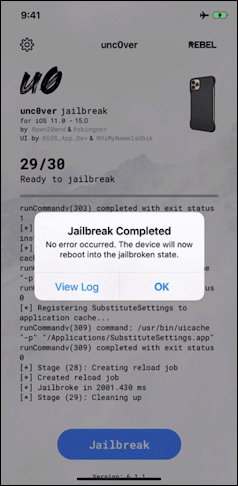
2. Unc0ver (Virtual)
Install the Unc0ver virtual jailbreak app to your iOS 15 – iOS 15.0.2 iPhone or iPad to get the iOS 15 Jailbreak experience. This is compatible with all latest devices including iPhone 12, iPhone 13 and latest iPads
Unc0ver virtual Jailbreak allows you to install lite versions of Cydia and this version does not provide all the jailbreak features. It has a very easy jailbreak process which does not access your device system root.
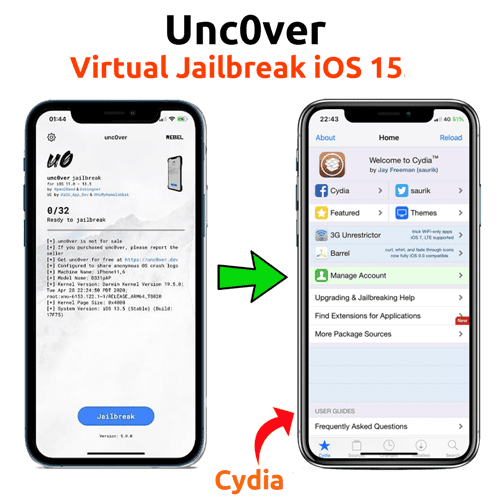
How unc0ver virtual works
Tap the unc0ver virtual download button. (bookmark) Then tap download v1.0.1 > English version. Complete simple steps to install the app store first and then find the Unc0ver Virtual app, tap on it. Once all done,it will appear on the Unc0ver virtual app device homescreen.
Open the Unc0ver virtual app, then tap on the Jailbreak button. Once complete the process, you can see the Cydia icon on your device homescreen.
More about Unc0ver
- Unc0ver is the best ever semi-untethered jailbreak tool up to iOS 14.8 jailbreak developed by Pwn20wnd and the Unc0ver team.
- Unc0ver original tool supports both Mac & Windows. Other than that, Online support was available.
- Unfortunately, unc0ver does not support iOS 14.8 onwards. Until Unc0ver supports the iOS 15, iOS 15.0.1 & iOS 15.0.2 jailbreak in future, users can jailbreak iOS 15 – iOS 15.0.2 using Unc0ver virtual app.
- The Virtual Unc0ver version is the only way to install Uncover on iOS 15 because the original Unc0ver tool does not support for iOS 15 & higher.
03. Cheyote virtual Jailbreak
Cheyote Jailbreak is the 1st rootless Jailbreak for iOS 15. But unfortunately, It is only compatible with iOS 15 – iOS 15.1.1 devices. So you can use Cheyote virtual as an alternative. You can install Sileo Jailbreak app manager as the default option using Cheyote. Also Cheyote virtual Jailbreak is compatible with all iOS 15 running device models such as iPhone 12, iPhone 13.

How Cheyote (Virtual) works
You can download Chyote from the above button. First download the Pangu8 store. Open the downloaded Pangu8 app store. Tap the GET button of the Jailbreak solution. Then tap on the virtual Cheyote tab to install the profile. Finally you can see the Cheyote Virtual app on your device homescreen.
Open the app, then tap on the Cheyote app, Tap the jailbreak button. You need to reboot the device to finish the jailbreak process. Once reboot you can see the Loader page. Tap on the Sileo icon to install the app. After a few seconds, you can see Sileo on the homescreen.
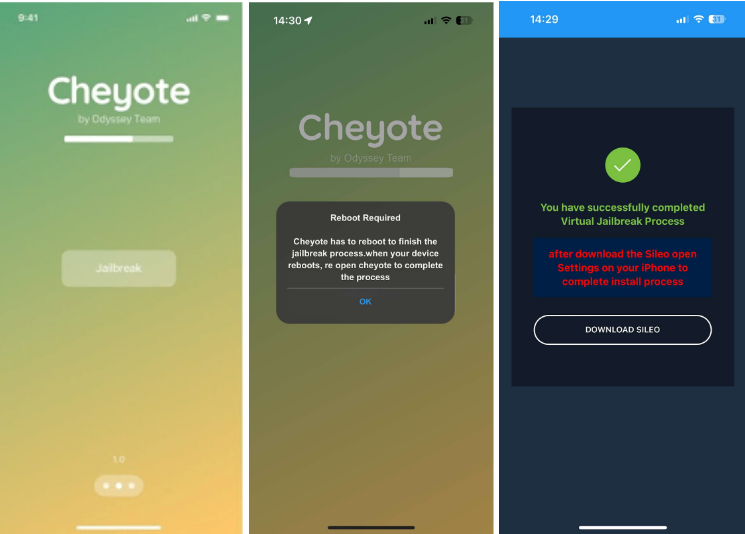
More about Cheyote
- Cheyote is the 1st rootless Jailbreak tool for iOS 15. Rootless jailbreaking is different from full-fledged Jailbreak. You can not access the System root through rootless Jailbreak, but don’t worry. You can do almost everything with a full-fledged Jailbreak from this Cheyote rootless Jailbreak
- Cheyote Jailbreak is developed by the Odyssey team. Coolstar, 23Aron, Tihmstar, Amy While and CRkatri Odyssey team has developed popular Odyssey Jailbreak for iOS 13 – iOS 13.7 and Coolstar has developed popular Electra Jailbreak
- Many popular Jailbreak tweaks such as Cylinder, Winterboard, dreamboard, ifile, Activator , Xen HTML Tweak will not work with iOS 15 with Cheyote.
- But some jailbreak tweaks/ apps like iCleaner, LottieNotifications, Photon, Asteroid will work with iOS.
- Most of simple jailbreak tweaks such as OverCharged, analogclock, Waktos, PowerDown will work with iOS 15 through Cheyote Jailbreak
4. Checkra1n (Virtual)
Now you can get a virtual iOS 15 jailbreak experience on any latest device using Checkra1n virtual. The Virtual Jailbreak process is very easy. It’s a completely online process, no need to use a Mac, Windows, Linux, any other OS, any other 3rd party software such as Altstore, Sildeloady etc. It’s let you install Checkra1n virtual app and jailbreak virtually to install Cydia, however can not get all the functions with this Limited Cydia
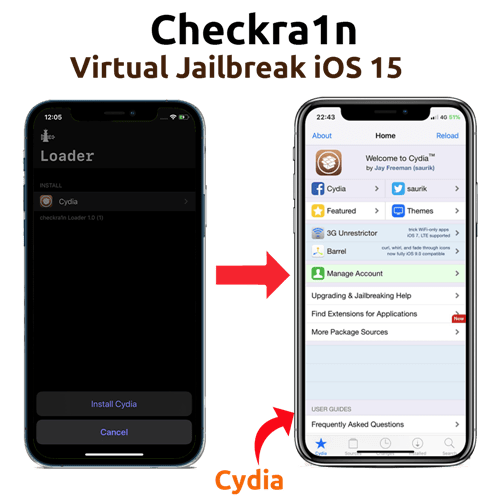
How Checkra1n virtual works
Tap the above button to install Checkra1n virtual, then “download now”, “English version”, go ahead with the initial installation process. Open the app store, then tap on the virtual Checkra1n tab to install the profile. Once you complete the installation process, you can see the Checkra1n Virtual app on your device homescreen.
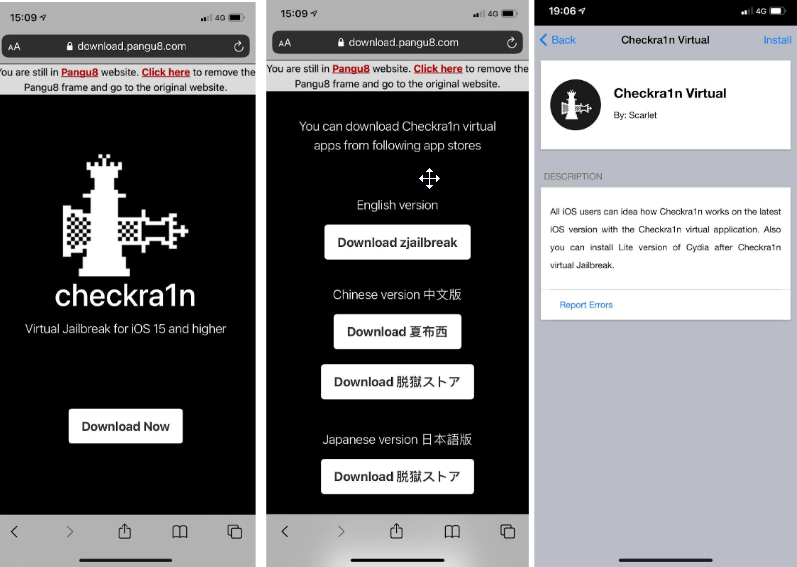
Open the app, then tap on the Checkra1n app, You can see the Loader page.Tap on the Cydia icon to install the app. After few seconds, you can see Cydia on homescreen.
More about Checkra1n Virtual
- Originally, Checkra1n was a permanent jailbreak based on the Checkm8 exploit released by axi0mX. It is a bootrom-level security exploit that can be used on iPhone 4S to iPhone X.
- Also, Checkra1n jailbreak does not support the latest devices such as A12, A13, A14 devices while checkra1n virtual supports
- Checkrain semi-tethered jailbreak is a computer-based advanced jailbreak method. Does not provide an online method. But Checkra1n virtual is a completely online process.
5. iBundles
iBundles service is a collection of premium websites that allows users to get almost every Jailbreak feature through 19 different websites. You can download themes, apps , tweaks and more from each iBundles partner website once you register with iBundels you can access all websites. It is a freemium service, but you can get it for free

How to get iBundles free
In iBundles, You can access 18 website based premium services after completing the one time payment.
But we believe that jailbreaking must be free, So we decided to publish free login details of iBundles from our website. Please check the following login details to log iBundles to download unlimited Jailbreak and 3rd party features for your iOS 15 running device.
Some of these logins may be blocked.
But make sure, you cannot get premium support for future iBundles updates using these login details, and don’t try to update these passwords.
Email – pamelaHSevier@dayrep.com
Password – JFA2244
Email – rebeccaTGrass42@yahoo.com
Password – JFA2244
Email – thomasAStoner@jourrapide.com
Password – NMC3033
Email – samsin2435@gmail.com
Password – MFA3641
Email – gegegdkekkhjhkwbw@gmail.com
Password – AJS2239
More about iBundles
- Unlimited access and unlimited downloads
- Most websites provide lifetime access and few websites provide five years membership
- All downloads are free from all of these websites
- All updates for future iOS versions and device models for free
- However, it’s not a free service. But don’t worry, using this you can get it for free.
More iOS 15 Jailbreak solutions
We have mentioned the most popular iOS 15 jailbreak solution at the top of the page. But there are more jailbreak methods for iOS 15. Check out below.
6. Jailscripting
Jailscripting is a siri scripting based method to install iOS 15 Jailbreak alternative tweaks. This is compatible with iOS 15.0.1 and iOS 15.0.2 as well as latest device models.

More about Jailscripting
- Jailscripting is the latest method to install Siri scripting-based iOS tweaks
- Jailscripting is a brand new method released in January 2022
- No computer needed to install tweaks and themes using Jailscrpting
- All themes and tweaks are verified and 100% safe to install
- It is very easy to install and uninstall Jailscrpting features, no device slowness or no void Apple warranty
- Jailscripting is a brand new method to install themes and tweaks for latest iDevices
- No hard installation process to follow. One tap installation allows you to install Jailscripting features
- All the iPhones running iOS 15 – iOS 15.3.1 and iPad models running iPadOS 15 – iPadOS 15.3.1 are compatible
- Colorful and awesome themes can be installed with Jailscripting.
7. TiJong Xūnǐ Jailbreak
TiJong Xūnǐ is a brand new iOS 15 and higher jailbreak solution. For the first time it was released in the Chinese version and now it is available to download the English version through the following link.

More about TiJong Xūnǐ
- All the iPhone models and iPad models are compatible.
- Both English and Chinese versions can be downloaded from the official site.
- Cydia 2 installs after the TiJong Xūnǐ virtual jailbreak process.
- You have to follow an easy online jailbreak process to install apps virtually.
- No need to worry about the device warranty.
- There is NO riks. (Risk free)
- All the iPhone models including iPhone 11, iPhone 12 and iPhone 13 are compatible with TiJong Xūnǐ
- Almost all iPad models running iPadOS 15 to the latest iPadOS are compatible
- Cydia 2 can be installed virtually as a Cydia alternative.
- Without accessing the device`s system root, it is possible to install iOS 15 jailbreak apps
8. Fugu 15
Fugu 15 is semi-untethered perma-signed Jailbreak for iOS 15 & higher versions. It was developed by Linus Henze and released as an open-source project some time back.

More about Fugu 15
- Runs Procursus bootstrap and Sileo Package manager
- No tweak injection method
- Fugu15 jailbreak only available for arm64e devices running iOS 15 – iOS 15.4.1
- There are two methods for setting up Fugu15 on your device, through USB or Safari
- Fugu15 Jailbreak for iOS 15 jailbreak uses the CoreTrust exploit / depends on a CoreTrust bug to bypass Apple Mobile File Integrity (AMFI)
- Designed for developers only, and it will never be updated for end user
- You don’t need a computer to re-jailbreak, but you will need to do so each time you reboot because it is semi-untethered.
- If you have a domain, you can install Fugu15 using Safari; otherwise, you can install it on a Mac using a USB connection and Xcode.
- As a TIPA package that can only be installed through TrollStore, Fugu15 was made available.
- Tested Devices and iOS Versions such as iPhone Xs Max: iOS 15.4.1, iPhone 11 (SRD): iOS 15.4.1, iPhone 12 (SRD): iOS 15.4.1, iPhone 12 Pro Max: iOS 15.4.1 & iPhone 13: iOS 15.1 (offline edition – see bugs below [WiFi bug])
9. Palera1n Jailbreak
Palera1n is a semi-tethered jailbreak for iOS 15 & higher versions. It is the first jailbreak tool for iOS 15 and still work in progress, but an experimental update available for all Chekm8 compatible devices.

More about Palera1n
- Must install Tips from the App Store
- First release has no tweak injection method, but now teaks supported
- This tool is developed by Nebula & Mineek.
- All repos work with the tweaks branch because it uses normal Procursus and not rootless.
- It was almost released as a developer-only jailbreak. Read more about the Palera1n jailbreak
- You must disable your passcode on A10 and A11 while jailbroken.Recommended only for advanced users only
- Even though tweak injection supported many jailbreak tweaks were not upgraded for iOS 16 but developed yet.
- Run futurerestore -exit-recovery or use irecovery -n if your device is stuck in
10. Xina A15 jailbreak
Xina A15 is rootless jailbreak for IOS 15 – iOS 15.4.1 A12-A15 devices. Currently it has released a test version.
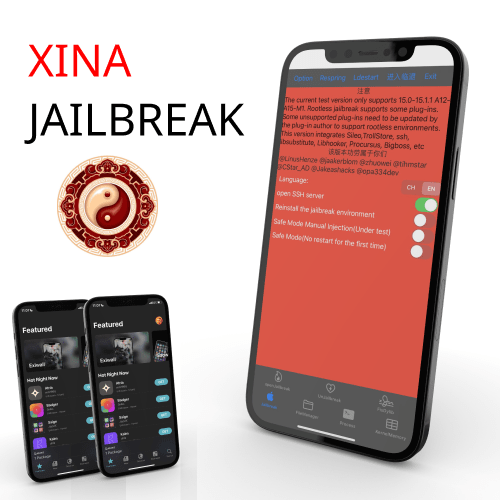
More about XinaA15
- It is highly recommended for developers only
- Easiest online method now supported with XinaA15
- Xina A15 jailbreak develop by @Xina520
- iOS 15 -15.4.1 A12-A15-M1 are supported now
- This is the first ever jailbreak for iPhone 13 models
- Download directly from zJailbreak app store, no need PC
- Try to repair the sileo language if there is a sileo 522 error
- This version incorporates Bigboss, Sileo, TrollStore, ssh, libsubstitute, and libhooker.
- IPA can be downloaded via official Github using Sideloadly or Altstore.
